
synced passkeys are stored in cloud-based password managers, which are phishable.
device-bound passkeys never leave the hardware and are effectively unphishable.
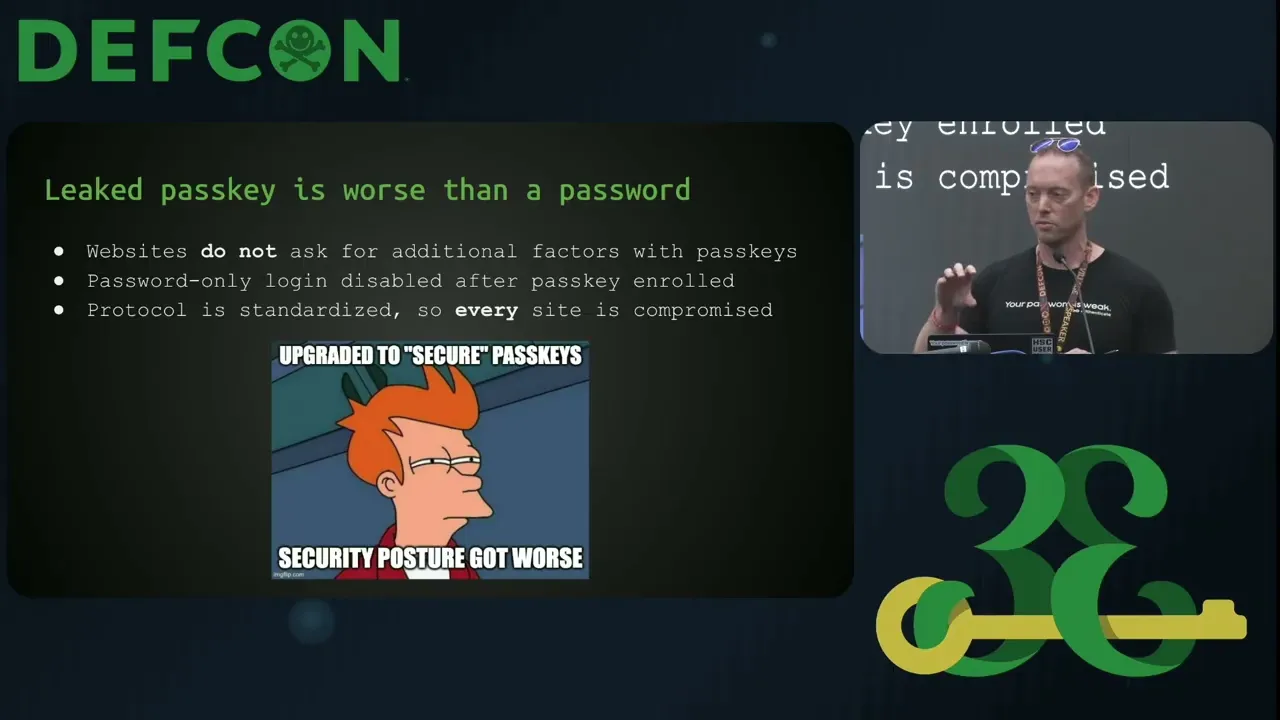
Synced passkeys are putting you at more risk than passwords and a second factor
If stolen, an attacker can use your passkeys to log in to your accounts without any other factor and they can steal your keys so that you can never log back in.
Cloud-based password managers are single point of failure — a compromise of the cloud-provider is the end
Synced passkeys are only as secure as the password manager credentials, which are phishable
Using the same key on every device means there is no redundancy or ability to remediate a single device
To highlight the risk, we demonstrate phishing attacks against two popular synced passkey providers
The attacks are easy to deploy and can successfully phish all of the users passkeys and passwords, which can then be exported and deleted to take complete control of the victims accounts
Check out our DEFCON 33 talk for more details
Device-bound passkeys – Keys are stored in the secure element (SE) of your phone and never leave. Nothing is synced to the cloud, exported, or stored on shared infrastructure.
Proximity-based authentication – Bluetooth LE challenge-response ensures access happens only when you’re physically present.
Multi-platform, no lock-in – Works across macOS, Windows, and Linux with native platform support
Rescue Missions – Secure decentralized backups of all of your keys using Shamir Secret Sharing (SSS) to backup your keys securely on the phones of your friends and loved ones
Free for personal use at download.allthenticate.com

Allthenticate
Smartphone-based passkey provider using device-bound keys stored in the secure hardware on the phone. The phone communicates over Bluetooth to paired computers to provide access to they keys across all of the user's devices without compromising security or usability.

Beyond Identity
Beyond Identity is enterprise identity provider that offers device-bound passkeys as well as other MFA and identity products.

HYPR
HYPR device-bound passkeys are a type of FIDO-based authentication credential designed specifically for enterprise environments, offering enhanced security and control over synced passkeys offered by platforms like Apple and Google.

KeePassXC
Local database storage, syncing is up to user.

Nitrokey
German-based provider of hardware-based USB and NFC passkey tokens. Nitrokeys are built using open-source hardware and software.

OFFPAD
Phishing-resistant FIDO2 security key with fingerprint-based, user-friendly authentication.

Solokeys
Open-source hardware security keys supporting device-bound FIDO2 credentials. Prioritizes transparency and tamper-resistance in hardware-backed authentication.

Swissbit (iShield Keys)
The iShield Key series is compatible with all FIDO2-compliant websites and services, such as Google, Microsoft, Salesforce, Amazon, and more. The all-in-one security key provides NFC and USB connectivity for versatile use. Stores up to 300 passkeys.

Token2 PIN+
Token2 PIN+ is an L2 certified security key with PIN complexity enforced.

Yubico (Yubikey)
FIDO2-certified hardware keys offering device-bound passkeys. Rated AAL3 by NIST, resistant to phishing, sync attacks, and physical compromise.

1Password
Syncs passkeys across devices for convenience, but this introduces risks of large-scale compromise tied to cloud storage and shared platform infrastructure.

Apple (iCloud Keychain)
Stores passkeys in iCloud and syncs across Apple devices. While secure by Apple’s standards, the architecture remains vulnerable to iCloud-based compromise and shared platform risk.

Bitwarden
Uses software-based passkeys stored in the cloud. While vault encryption is strong, synced credentials can still be exported or exploited if the cloud account is compromised.

Dashlane
Password manager that lets users store passkeys — protected by username and password.

Google Password Manager
Syncs credentials across Google services and devices, introducing attack surfaces tied to Google account takeover and centralized cloud storage.

KeePassXC
Local database storage, syncing is up to user.

LastPass
Relies on synced passkeys, leaving users exposed to threats like platform-wide breaches and unauthorized data sharing between cloud-linked devices.
Microsoft EntraID Synced Passkeys
Phishing resistant passkeys are phishable if users are allowed to use synced passkeys via MS Authenticator on BYOD
Even if you take nothing else away from this piece, if your organization is evaluating passkey deployments, it is insecure to deploy synced passkeys.
Ravie Lakshmanan
The Hacker News
Oct 15, 2025
Researchers showed how hackers could steal and reuse your passkeys by tampering with the browser itself — even making the login look completely normal. Their work highlights why passkeys aren’t foolproof and why extra protections are still needed.
Shourya Pratap Singh, Jonny Lin, Daniel Seetoh
SquareX / DEFCON 33
Aug 4, 2025
Dan argues that synced passkeys are no better than passwords that "must" be stored in a password manager. Nicely articulating the exact attack that we demonstrated.
Dan Fabulich
Choice of Games
Aug 4, 2025
PoisonSeed demonstrates a QR-based phishing method that tricks users into approving FIDO2 logins without a security key.
Lawrence Abrams
Bleeping Computer
Jul 19, 2025
This paper demonstrates how a Man-in-the-Middle attack can exploit the Client-to-Authenticator Protocol (CTAP) in passkey authentication, enabling an attacker to hijack a victim’s session via Bluetooth and gain account access. The findings underscore the need for stronger safeguards in future FIDO and WebAuthn implementations.
Donghyun Kim, Junseok Shin, Gwonsang Ryu, Daeseon Choi
IEEE Access
May 15, 2025
Tobia Righi reveals a vulnerability that allows passkey phishing via fido:/ URIs over Bluetooth, affecting mobile browsers.
Tobia Righ
CVE-2024-9956
Feb 24, 2025
This arXiv paper compares device-bound vs synced passkeys, highlighting how syncing can introduce phishing risks in FIDO2 systems.
Andre Büttner, Nils Gruschka
University of Oslo
Jan 13, 2025
Accenture’s Red Team shows how attackers can spoof Windows Hello for Business to bypass passwordless authentication.
Yehuda Smirnov
Accenture / Blackhat 2024
Aug 8, 2024
Back in 2023 Lauren Weinstein was highlighting the attack shown here and sounding alarm bells. Here we are in 2025, with the same problem.

